Complete UAF exploit - UD Capture
Por um escritor misterioso
Descrição

Automated Use-After-Free Detection and Exploit Mitigation: How Far
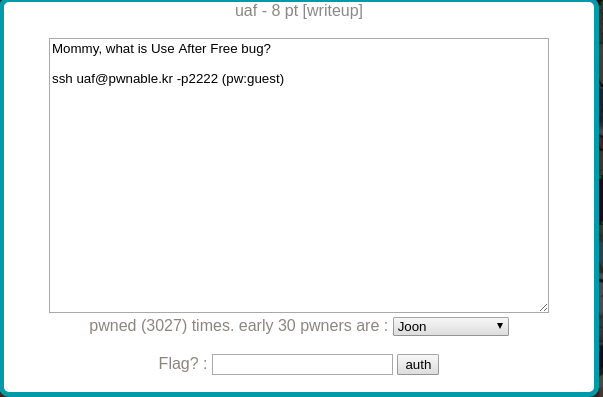
uaf' — CTF by pwnable.kr. So, for those of you who don't know
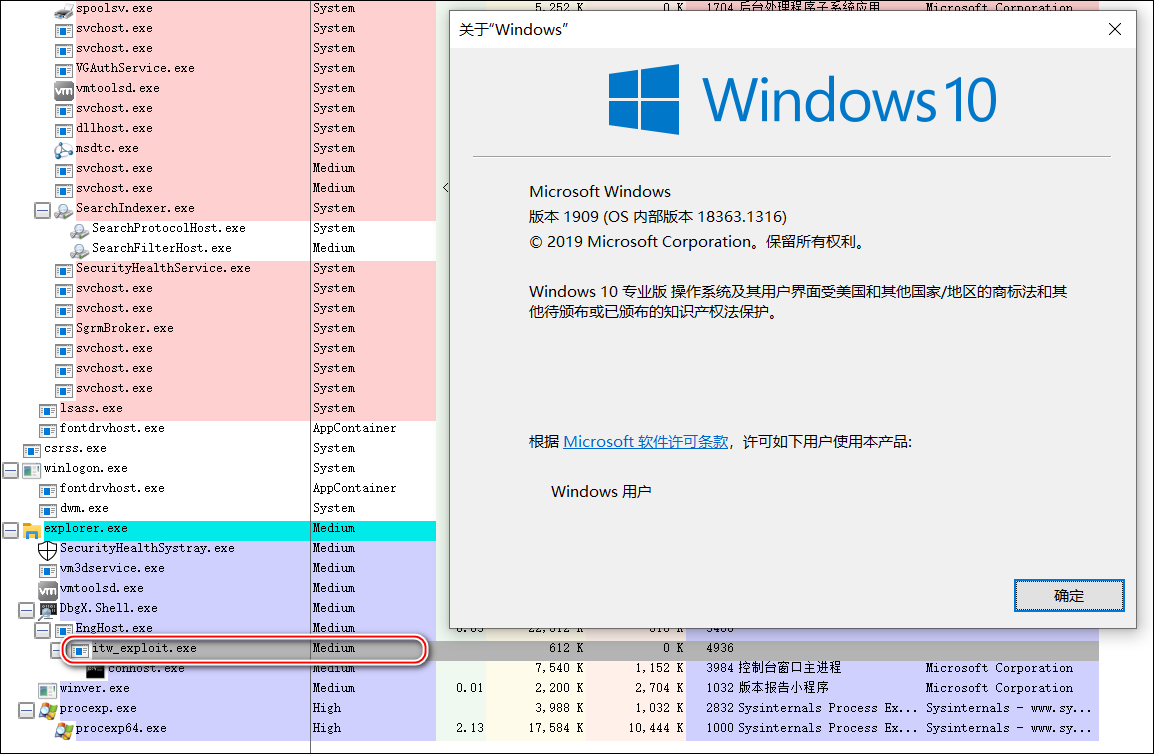
安全星图平台

General David H. Petraeus, US Army (Ret.) on LinkedIn

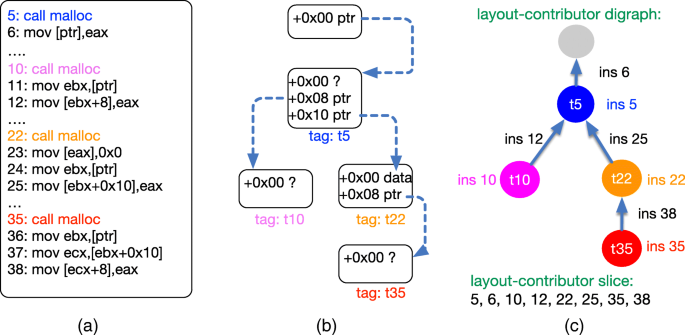
UAF-GUARD: Defending the use-after-free exploits via fine-grained
From proof-of-concept to exploitable, Cybersecurity
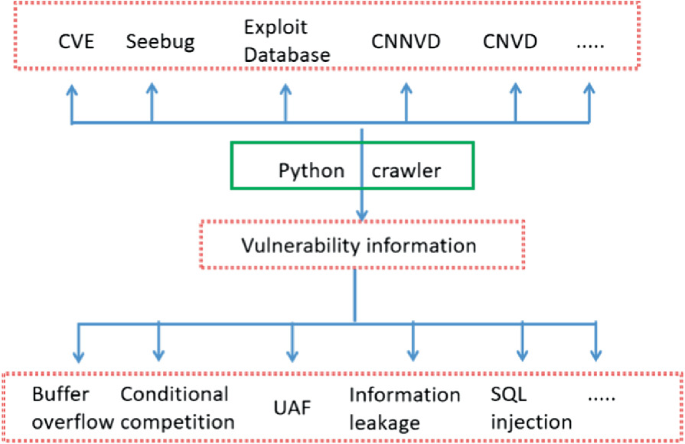
Establishment of Vulnerability Sample Database in Network Attack
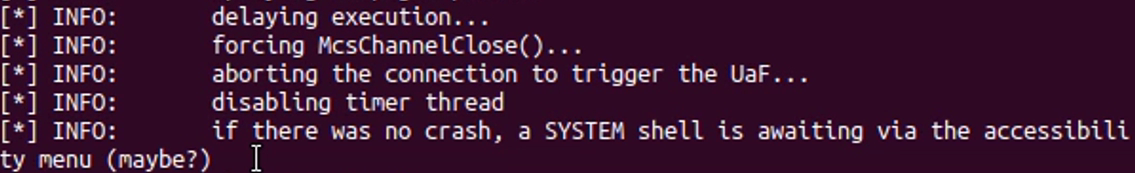
BlueKeep PoC demonstrates risk of Remote Desktop exploit – Sophos News

HITB2022SIN Exploiting A Limited UAF On Ubuntu 22.04 To Achieve
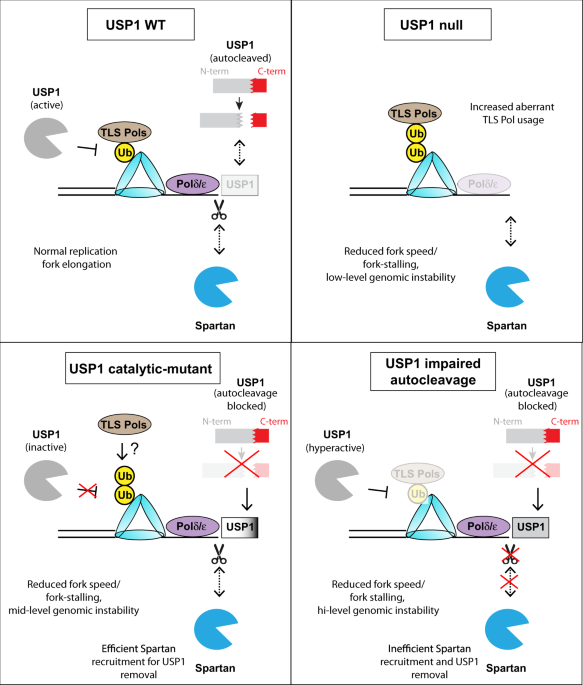
USP1-trapping lesions as a source of DNA replication stress and
de
por adulto (o preço varia de acordo com o tamanho do grupo)