Hacker Simulator - Succeed 5 Phishings
Por um escritor misterioso
Descrição
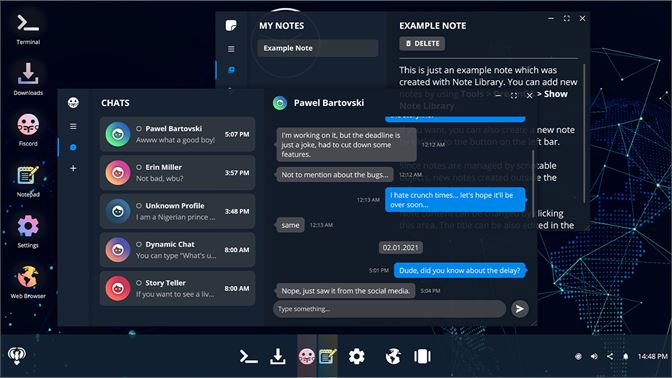
scansystem and scanfolder have been replaced by the ls commandI edited out the time between contracts, the time it takes for them to respond on fishbook, and

Phishing Arctic Wolf

Measure Your Organization's Cyber Secure Culture

19 Examples of Common Phishing Emails

How to Use a Phishing Simulation to Train Employees - Total Security Advisor
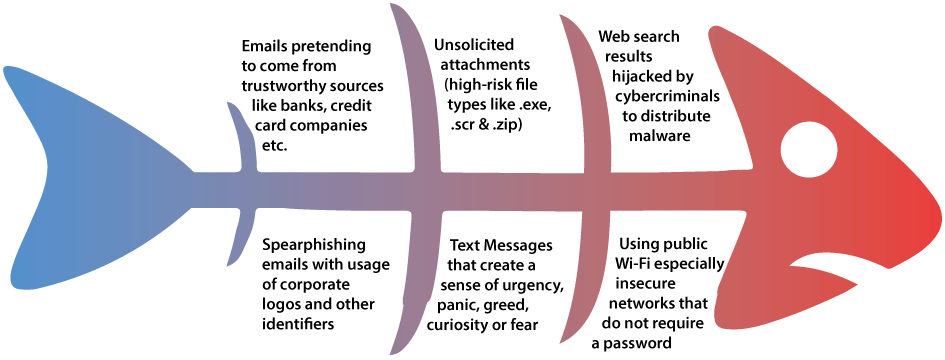
Preventing SMiShing, SMS phishing
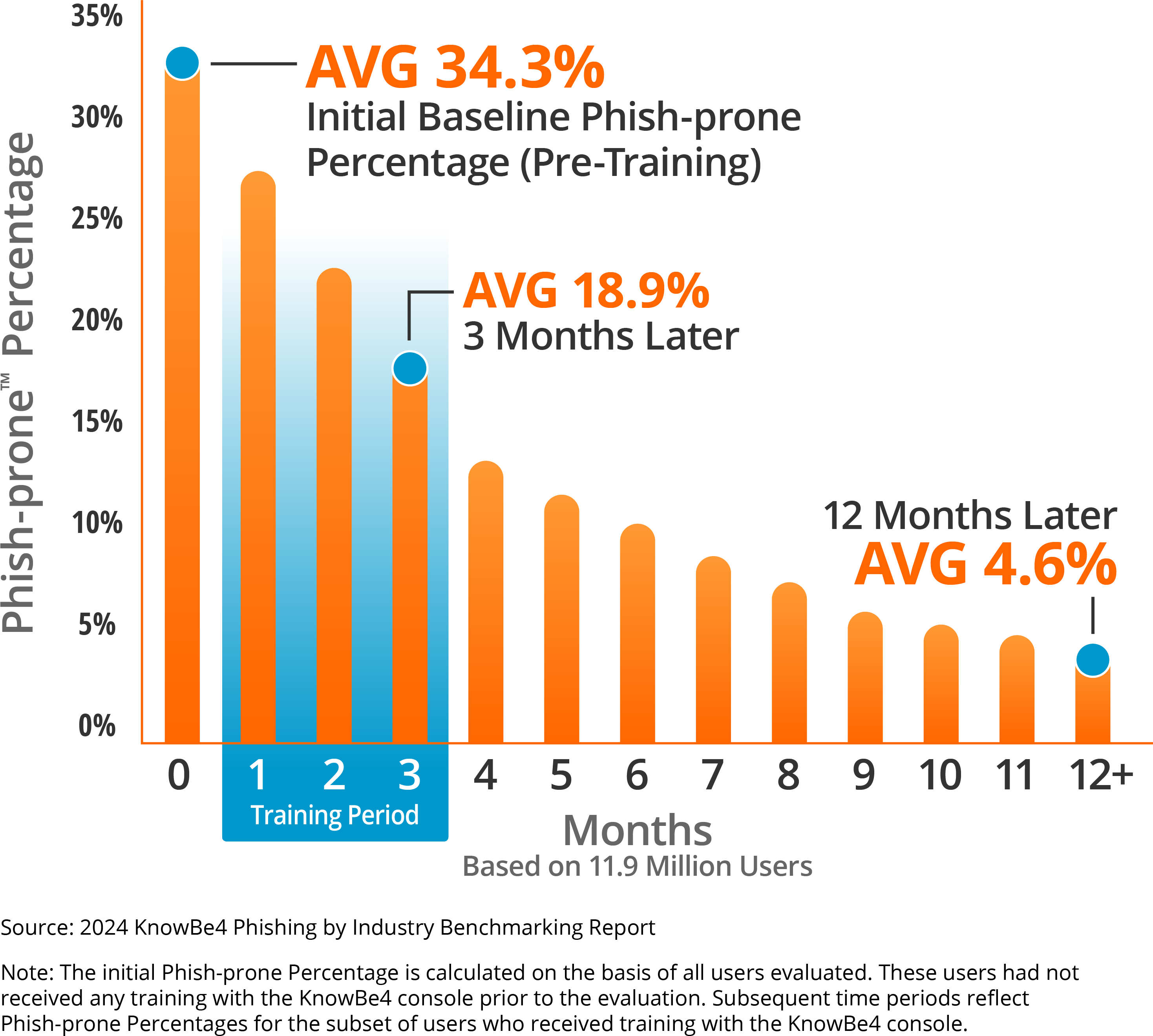
Security Awareness Training

What Is a Phishing Email Attack? Definition, Identification, and Prevention Best Practices - Spiceworks

The Coming AI Hackers Belfer Center for Science and International Affairs
Guide to phishing simulation tools

Avoid the Spear: How to Protect Yourself from Spear Phishing Attacks
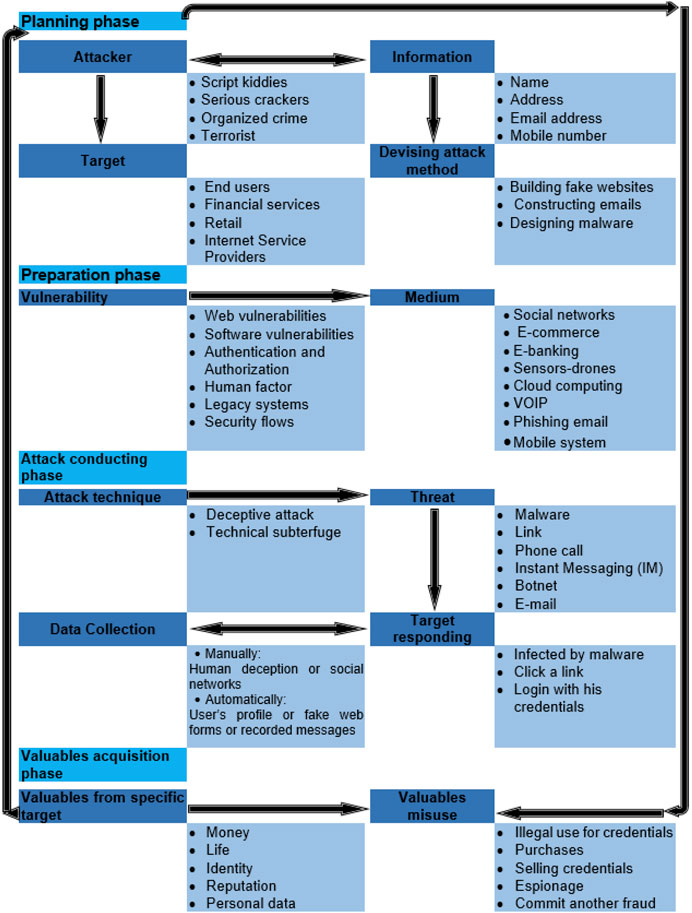
Frontiers Phishing Attacks: A Recent Comprehensive Study and a New Anatomy
de
por adulto (o preço varia de acordo com o tamanho do grupo)