Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Robust Malware Detection Models: Learning From Adversarial Attacks and Defenses - Forensic Focus

Malware Analysis - What is, Benefits & Types (Easily Explained)

What is Malware? Definition, Types, Prevention - TechTarget

Cybersecurity Search Engine

MetaDefender Cloud Advanced threat prevention and detection
Malware Analysis - What is, Benefits & Types (Easily Explained)

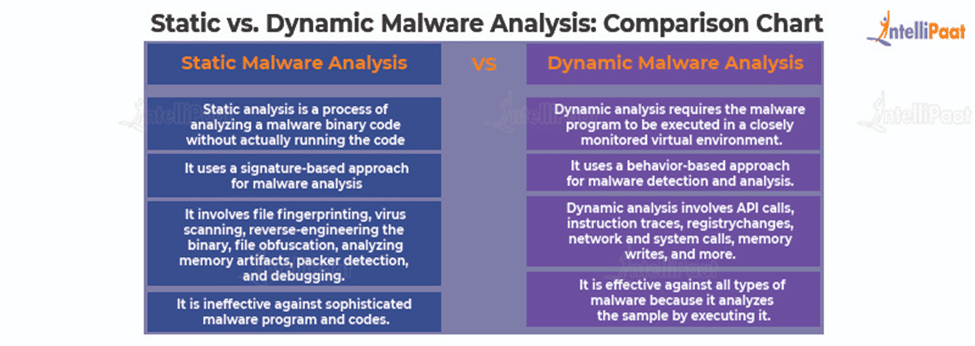
How to Do Malware Analysis?

Top 10 Types of Information Security Threats for IT Teams
Lab 6-1 Solutions - Practical Malware Analysis [Book]

Malware analysis mykey_.rar Malicious activity

How to Analyze Malware's Network Traffic in A Sandbox
de
por adulto (o preço varia de acordo com o tamanho do grupo)